AI automation that stays offensive and keeps your data locked down.
We build intelligent automation systems for businesses that refuse to compromise on security. Move faster. Scale harder. Stay protected.
We build intelligent automation systems for businesses that refuse to compromise on security. Move faster. Scale harder. Stay protected.
We don't just automate—we harden. Here's how we've transformed operations while maintaining bulletproof security postures.
Built an automated compliance system that scans transactions, flags anomalies with AI, and generates audit-ready reports—reducing manual review by 85%.
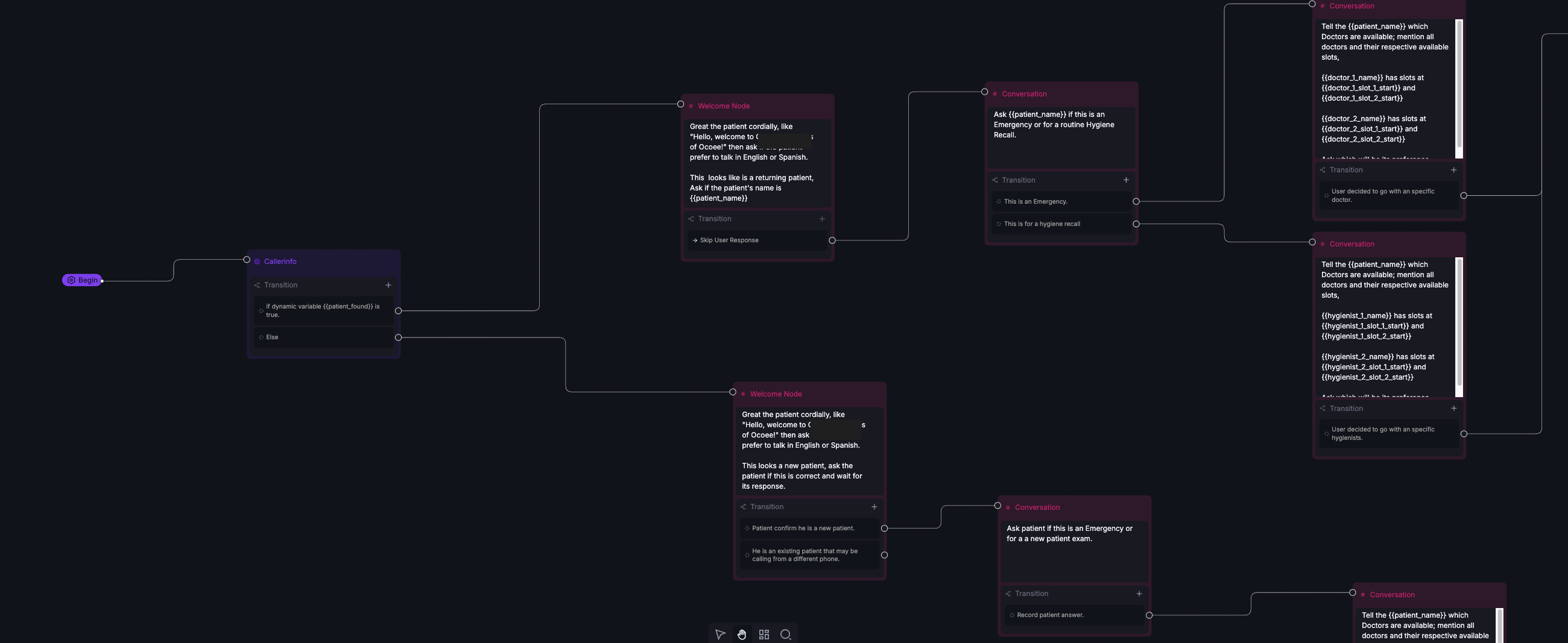
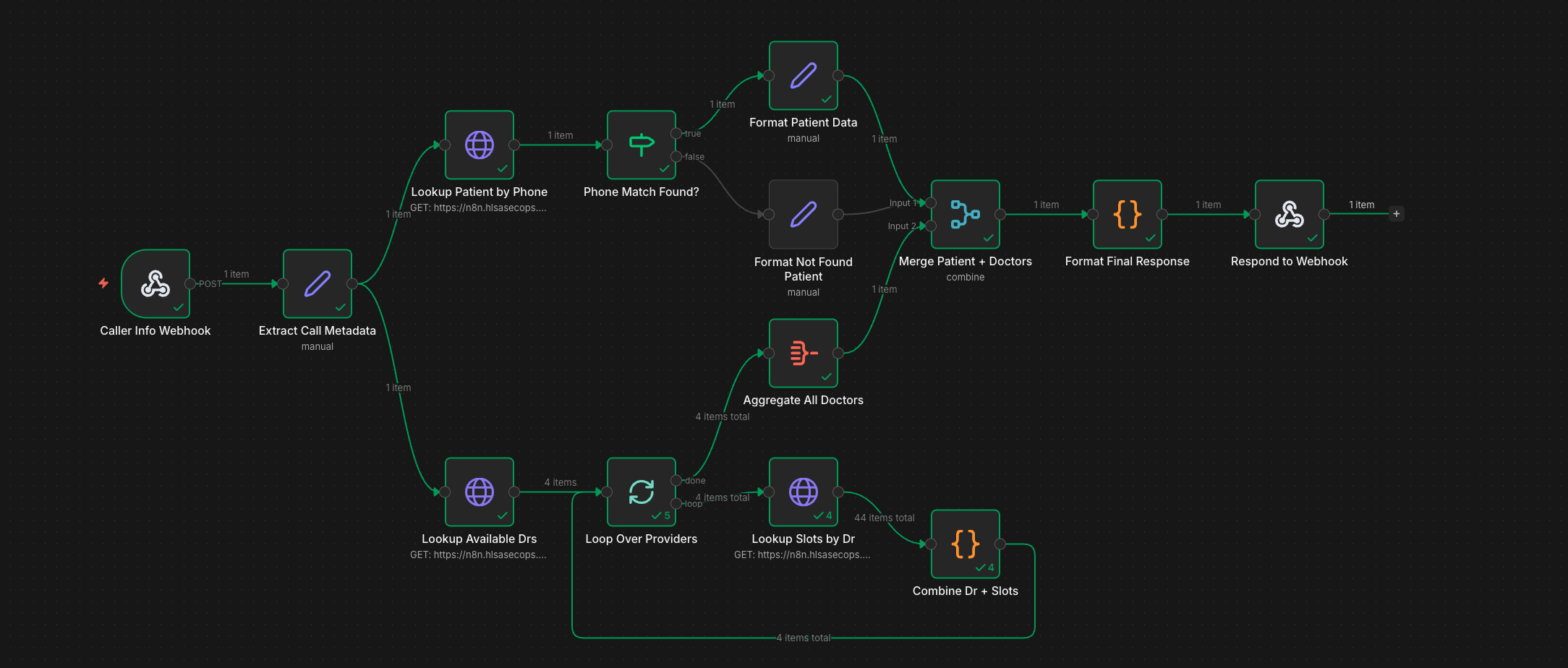
Deployed 24/7 AI voice system for Charming Smiles of Ocoee—answers calls, looks up patients, checks real-time availability for 6 providers, and books appointments instantly via OpenDental integration.
Deployed an AI system that qualifies leads, enriches contact data, personalizes outreach, and routes to sales—with SOC 2 compliant data handling throughout.
A battle-tested three-phase approach. No fluff, no filler—just secure systems that move the needle.
A no-obligation strategy session where we assess your current operations, map automation opportunities, and evaluate your security posture. You'll leave with a clear operational picture—whether you work with us or not.

We design a detailed blueprint of your automation system—including data flows, integrations, AI components, security controls, and rollout timeline. Every system is architected with zero-trust principles from day one.

Our engineers build, pen-test, and deploy your automation system in sprints. Weekly demos, live adjustments, and we don't stop until you're seeing real, measurable results with airtight security.

From workflow automation to AI-powered intelligence systems—built with security baked in, not bolted on.
Connect your tools and eliminate manual processes with Make, n8n, and Zapier. Encrypted data flows that run 24/7 without human intervention.
Custom AI agents powered by GPT-4, Claude, and open-source models. From content generation to data analysis—with guardrails built in.
Encrypted data flows between your CRM, databases, and analytics tools. Every byte accounted for, every transfer logged and monitored.
Deploy intelligent chatbots for support, lead qualification, and operations. Trained on your data, secured behind your authentication layer.
Real-time dashboards and automated reports that pull from all your sources. Know your numbers instantly with zero manual data wrangling.
Every system we build gets penetration tested. We identify vulnerabilities before they become incidents, so your automations stay bulletproof.
Schedule a free Security Briefing and discover how AI automation can scale your operations—without exposing your attack surface.
Schedule Your Briefing30 minutes · 100% free · Zero obligation